The answer is in the first comment, and it may not be what you expect. Take a moment to read it carefully before jumping to conclusions, because small details can change the whole picture and completely shift how the situation is understood.
“Test your math skills.” It’s a phrase designed to feel light, almost effortless, as if it’s inviting you into a quick mental warm-up rather than a serious…
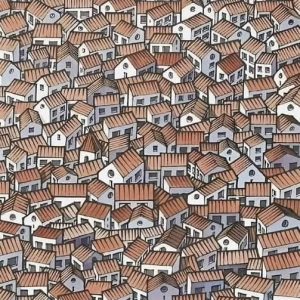
Can you spot the hidden cat? This visual puzzle challenges you to look closely, as many people miss it at first glance. Careful observation and attention to small details are key to finding what’s cleverly concealed in the image.
This kind of visual illusion works because it takes advantage of how the brain processes patterns and filters information. At first glance, the rooftops appear uniform and…

If you have visible veins, it often relates to lower body fat, lighter skin tone, exercise, aging, or good circulation. In most cases, visible veins are normal and not a health concern.
Visible veins are a common physical feature that often draws attention, especially on the hands, arms, legs, or feet, and can sometimes cause unnecessary concern about circulation…
Visual logic puzzles are best approached by focusing on structure rather than meaning. Start by identifying patterns, repetitions, and changes in shape, position, or quantity. Work step by step, test simple rules first, and avoid reading hidden symbolism into the images unless the puzzle clearly suggests it.
“Which truck is braking?” style puzzles are popular because they look straightforward but actually rely on careful visual interpretation rather than quick intuition. At first glance, the…
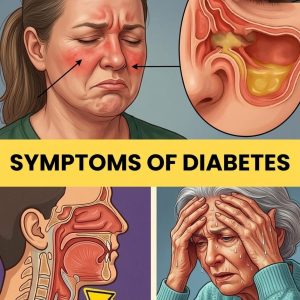
Early symptoms of type 2 diabetes often develop gradually and can be easy to miss. These may include increased thirst, frequent urination, fatigue, blurred vision, slow-healing wounds, and increased hunger. Early screening, healthy lifestyle choices, and medical advice are important for proper diagnosis and management.
Type 2 diabetes is a chronic metabolic condition that often develops gradually and silently, making it difficult to detect in its earliest stages. It is primarily characterized…
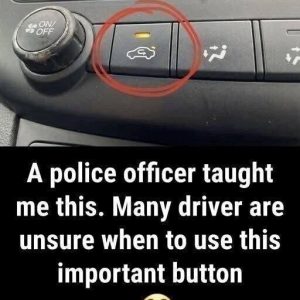
The air recirculation button in your car controls whether air from inside the cabin is reused or replaced with outside air. When activated, it improves cooling efficiency, helps block odors and pollution, and can make your driving experience more comfortable in heavy traffic or hot weather.
Most drivers have seen the dashboard icon showing a car with a circular arrow, but many are not fully aware of what it does. This symbol controls…

What a tragedy—the whole country is mourning this loss. The news has left many shocked and emotional, and people are sharing their grief and memories as they wait for more details to emerge.
A quiet Missouri town, Defiance, was shaken by a devastating tragedy when a sudden house explosion and fire claimed the lives of two young brothers, Julian, 4,…
Choose a nail and discover what kind of woman you are through this fun personality idea. The shape or design you’re drawn to may reflect traits like confidence, creativity, elegance, or independence. While not scientific, it can be an entertaining way to explore what your choices might say about you.
This personality test uses nail design preferences as a playful way to explore possible connections between aesthetic choices and personality traits. It suggests that the designs people…
Seven psychological reasons can explain why some children emotionally distance themselves from their mothers, often tied to identity formation, safety, guilt, unmet needs, and cultural pressure. These patterns reflect coping mechanisms rather than cruelty, and understanding them can support healing, boundaries, and healthier relationships.
There is a form of grief that many mothers experience quietly over time, often without a clear name. It is the emotional pain of feeling that a…

If you are over 50, eating a banana every day can support overall health and well-being. Bananas provide potassium, fiber, and vitamins that help heart health, digestion, and energy levels, while contributing to strength, balance, and vitality as you age.
As people move beyond 50, the body begins to change in gradual, often subtle ways. Energy levels may dip earlier in the day, muscles can feel more…